Smart Applications 8000212345 Techniques
Smart Applications 8000212345 Techniques integrate data, automation, and user-centric design to enable scalable, adaptive workflows. They combine AI, analytics, and context-aware interfaces with governance and provenance. Architecture favors modular patterns across cloud and edge, balancing central processing with local responsiveness. Security and privacy remain foundational, guiding deployment and innovation. The approach prompts questions about tradeoffs, resilience, and trust, inviting further examination of how these techniques transform real-world solutions.
What Are Smart Applications and Why They Matter
Smart applications integrate data, automation, and user-centric design to solve real-world problems more efficiently than traditional software.
They orchestrate lines of insight across devices, enabling scalable workflows and adaptive interfaces.
This approach emphasizes autonomy and resilience, inviting experimentation.
Core Techniques: AI, Analytics, and Context-Aware Design
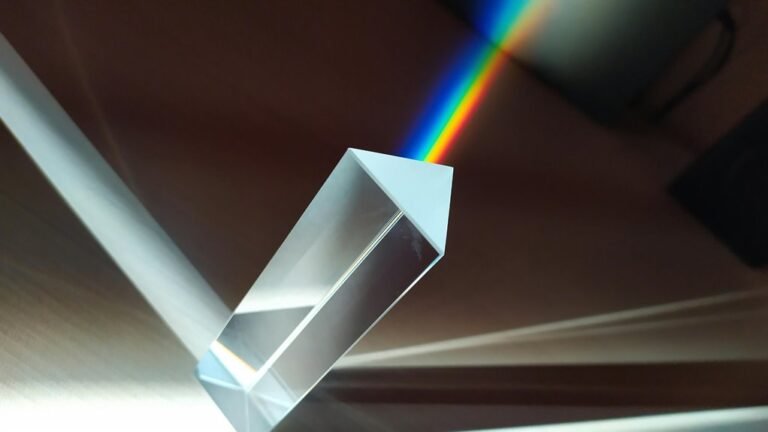
The interplay of AI, analytics, and context-aware design shapes how smart applications operate across devices and environments. This convergence enables adaptive experiences while demanding disciplined governance: AI governance frames responsibility and accountability; data provenance ensures traceable inputs and transformations; edge intelligence distributes processing to preserve responsiveness; privacy preservation safeguards user control, fostering trust without compromising analytic capability.
Architecting for Cloud and Edge: Architecture Patterns and Tradeoffs
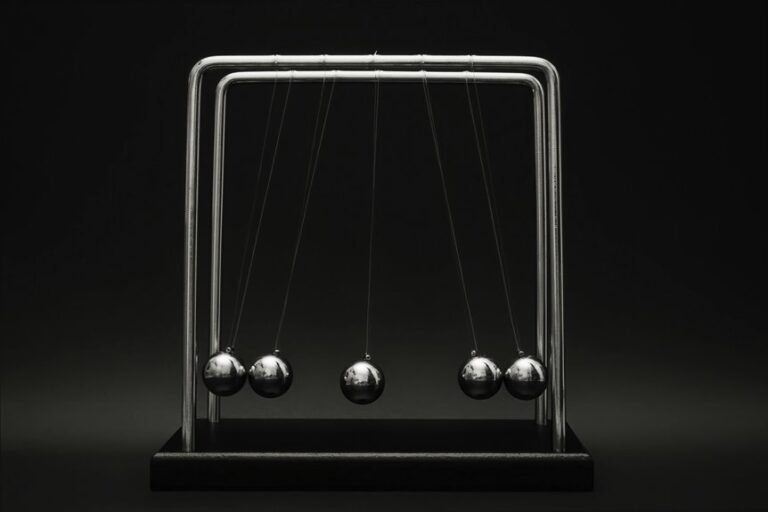
The analysis compares design patterns for latency, resilience, and scalability, highlighting deployment tradeoffs between centralization and local processing.
It emphasizes modularity, observability, and adaptability, guiding designers toward flexible architectures that balance autonomy with coordination and freedom.
Security, Privacy, and Real-World Use Cases You Can Apply
How do security and privacy constraints shape real-world deployments of intelligent applications? The discussion examines governance, consent, and risk management as enabling constraints rather than barriers. It highlights modular architectures, Data Minimization, and privacy-preserving analytics. Real world use cases reveal tradeoffs between performance and protection, guiding design choices toward transparency, trust, and adaptable security postures, with security privacy guiding ongoing innovation.
Conclusion
Incredibly, smart applications promised flawless autonomy, yet here we are verifying every data packet for provenance and privacy. The architecture glitters with edge-ability, but hinges on governance and transparent design more than flamboyant AI. Analysts obsess over cloud-edge tradeoffs while users quietly demand resilience and privacy. So yes, the future runs on adaptive interfaces and robust analytics—ironically, only as long as we enforce discipline, governance, and real-world accountability, not just clever abstractions.